With Christmas and the holidays behind us, we still have the added complication of COVID-19. This fact has not been lost on cybercriminals, the “bad guys” who are always trying to steal your identity by tricking you into giving up some of your personal information. So, now that you may have a little less time pressure on you, let’s take a minute to review some basic online safety measures to keep you as safe as possible while enjoying time with family and friends (probably virtual), and of course, online SHOPPING!
The CDC and your local government have provided medical guidelines for safe interactions during COVID, but we’re talking about cyber health and what you can do to add a layer of safety and confidence to your online interactions.
Who are the “bad guys”?
Just who are these cybercriminals? They can be young or middle aged, mostly male but also female, any nationality, and they could be next door or on the other side of the world. Most do it for money, but some do it just because they can; for fun and bragging rights. The important point is that they are smart and have the tools that make it easy to exploit any of your online accounts or transactions that aren’t well-protected.
What’s at stake?
Being careless or just unaware of proper online safety can allow a cybercriminal, the “bad guy”, to steal your credentials like passwords, social security number, bank account logons, etc. Here are some of the bad things that they can do:
- Credit card fraud—use your information to make charges on your credit card
- Ransomware—lock your computer files and extort you for money
- IoT threats—compromise a router or connected camera
- Account takeover—use your credentials to make online transactions on your behalf
- Identity theft—steal your identity and act on your behalf
- They could even steal the title or deed to your home!
According to Fool.com, 2019 was the worst year in history for identity theft, and 2020 has not been better so far.
Are you a target?
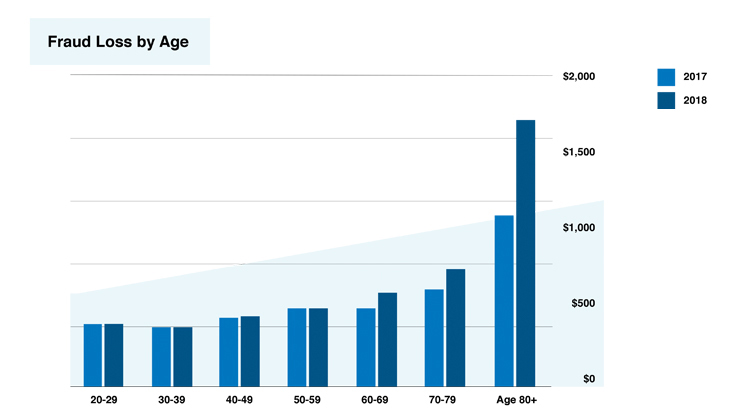
If you have a social security card, you are at risk for identity theft. These bad guys target the young, the old, and everyone in between. It turns out that most of the identity theft occurs within the 20-49 age group, because they have more credit cards and they purchase more online. However, when it comes to fraud reports other than credit cards, most of that occurs in the 60-69 age group. The most likely reason is that people become more trusting as they age. Check out this chart showing the average fraud loss amount by age.
Younger adults lose money to fraud more often, but when older people experience a fraud-related financial loss, the median amount is much higher, according to the Federal Trade Commission. Source: 2020 Identity Theft Statistics | Consumer Affairs
What are the COVID-related things they’re doing?
According to IdentityForce, the most common COVID-19 scams in 2020 include:
- Fraudulent e-commerce vendors for masks, sanitizers, and test kits
- Fraudulent investment sites
- Phishing (email) and vishing (voice calls) through update emails, texts, and voicemails
- Spoofed government and health organization communications
- Fake vaccines or “miracle cures”
- Scam employment posts
- Phony charity donation offers
What you can do
Keep your antivirus software up to date
If you don’t do anything else, make sure you have an antivirus installed on your computer and keep it up to date. For Microsoft Windows, you should be on version 10, where Microsoft Defender Antivirus (formerly called Windows Defender) is the default and is actually pretty good. And, it’s free and easy to use. If you feel that you need more, there are numerous apps available.
Check your bank account transactions regularly
If you regularly balance your checkbook and check your bank statement, you’re ahead of the game on this point. Often the cybercriminal will steal your credit card information and begin making small purchases from the same places that you do. These small amounts add up over time but may not be caught by your bank or credit card company. If you see transactions that you did not make, call your bank or credit card company immediately!
Password manager—you need one
If your passwords are easy to remember, they’re probably too weak. Basically, short passwords are weak; long passwords are strong. When it comes to passwords, the longer, the better. Also, you should never use the same password twice. If you’re thinking “There’s no way. I can’t remember long passwords!”, you’re right. That’s why you need a password manager. You create one very long difficult pass phrase that you can remember. Then you use that to unlock the password manager, which stores all your other passwords.
For the iPhone and Apple products, use the iCloud Keychain. This is great for Apple products, but unfortunately, it doesn’t easily adapt to a PC.
Here are a few good password managers: RoboForm, Keeper, LastPass, DashLane, Bitwarden, LogMeOnce, etc. Most of these don’t cost much, but they are extremely important for keeping your passwords organized and safe. Most of these can sync your passwords across all your devices, which is a must if, for example, you shop Amazon on your iPhone and your PC.
MFA!
Today, even a good password is not enough! Weak passwords can be guessed; strong passwords could be stolen. The solution is multi-factor authentication (MFA). Simply put, MFA is short code or number that is sent to you in a text or email in addition to your password. For example, you go to your bank website to logon. You enter your username and password. Next, they send you a code that you must enter into a box on their site. This verifies that it was really you who is signing in; the “bad guys” will not have the code even if they had your password.
What we’re doing
At Spectrum, we’ve also felt the impact of the pandemic, and we’re doing our part. We’ve tightened our security stance to protect your data and ours. Here are some of the specific things we’re doing to protect your information:
- Our “Client Portal” protects you by avoiding sending personal info in email
- Our “Prospect Portal” similarly protects prospective clients
- Diligent email filtering, monitoring, and user training
- MFA where possible
- Business Continuity and Disaster Recovery testing
- Masks, social distancing, and hand washing
- Regular office sanitizing
Together we can make our online experiences safe and profitable in 2021.